Advanced Data Recovery Tutorial of Encrypted WD USB Drives
Decryption video link of encrypted WD USB drives:
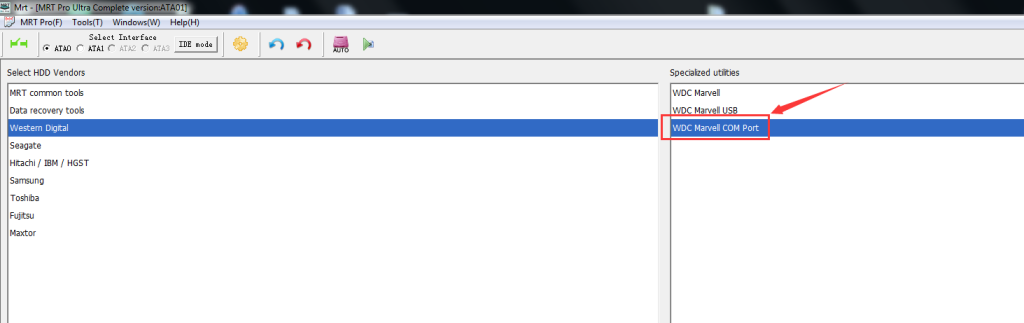
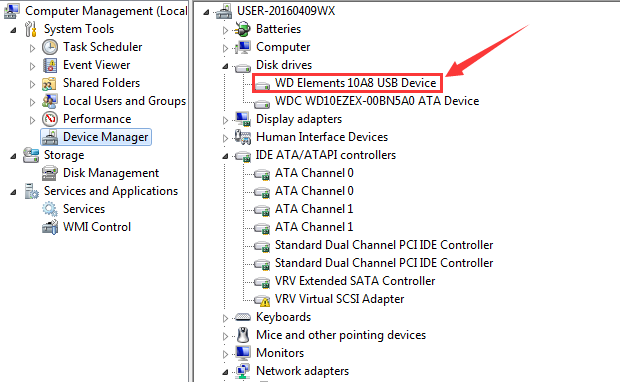
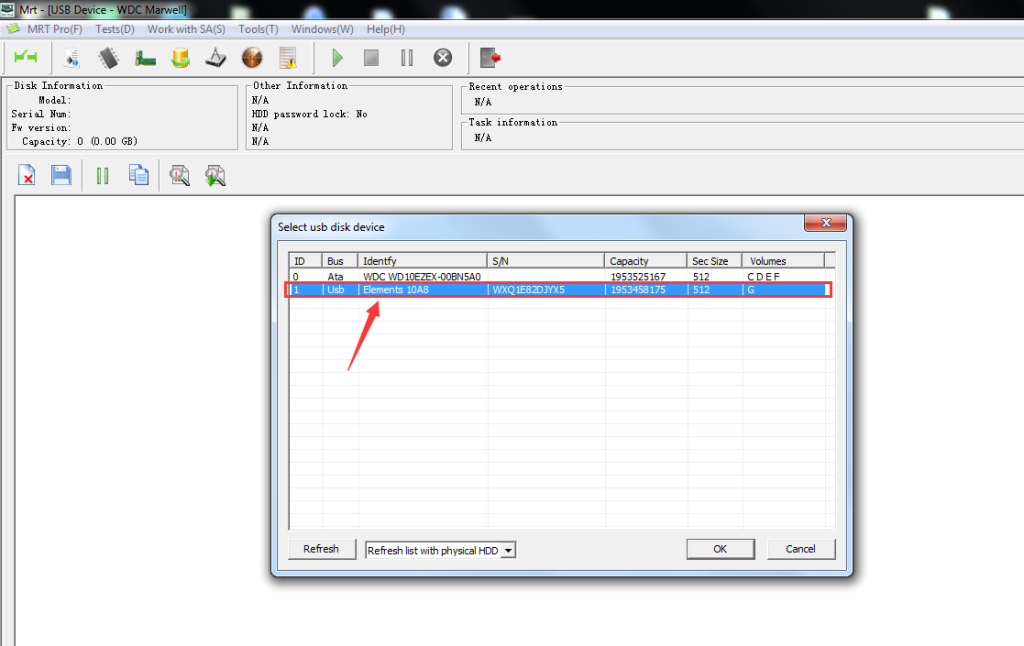
http://us.mrtlab.com/video/wdcusbdecryptionen.rarCurrently, WD portable hard disks are with interface of USB2.0 or USB3.0. And a USB cable is needed if we want to get stored data. One side of the cable is connected to portable disk, while the other side is connected to computer’s USB port. In MRT software, there is one special utility called WDC Marvell USB. The basic requirement when using this utility is that WD portable disk can be detected by operating system. Which is to say, when the disk is connected to computer, it should be found in “Device Manager”, or we can not use WDC Marvell USB utility when it is undetectable in operating system. As shown in pics:
WD portable USB drive is directly connected to host computer via USB cable, so that we can not execute operations like power off/on, soft reset, hard reset and skipping when native USB interface is used. So when facing with bad tracks or bad sectors, the disk will keep long time busy or even get stuck, which will largely affect the speed and quality of the image. The example we have mentioned just now is the situation that the disk can be detected normally by computer, for those which can not even be normally detected by operating system, does it mean no any chance at all? Absolutely, the answer is no.
When the above situations occur, we can try to convert USB interface into SATA interface, so that we can try to connect the disk to MRT hardware card. For disk with bad sectors, we can set error handling parameters in DE utility; for undetectable disk, we can try to fix it under firmware level first, then do the image.
Part One: How to convert USB interface into SATA interface
The first method is to replace PCB board directly:
If we want to replace USB PCB board directly, we need to find the corresponding SATA board first, here is the pic of comparison table of WD 2.5′ portable USB PCB number to its corresponding SATA PCB board number:

After getting corresponding SATA PCB board with same MPU chip, we need to remove the ROM chip from USB PCB board and then weld it to SATA board; or we can use programmer to read out the ROM data and save it, and use software to write the saved ROM data to the chip of SATA board. We need to screw up the SATA board in the end.
The second method does not need to change PCB board, but we have to solder wires:
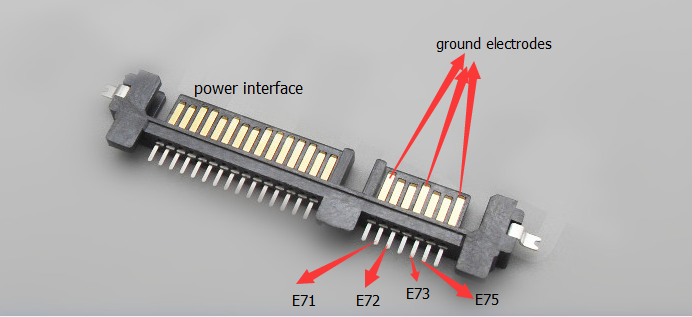
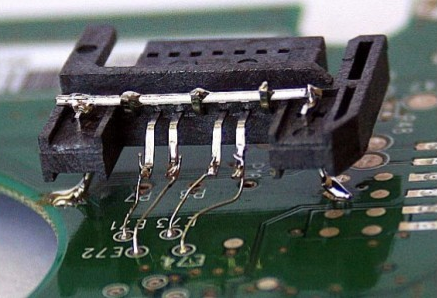
Before soldering wires, we need to locate four points on the USB PCB board, they are E71, E72, E73 and E75. The pins of these four points belong to data interface pins, as shown in the pics:

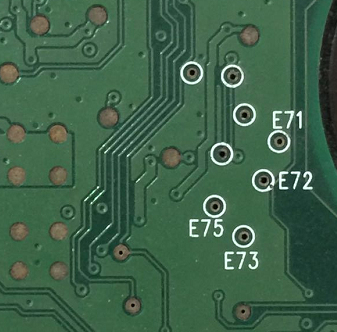
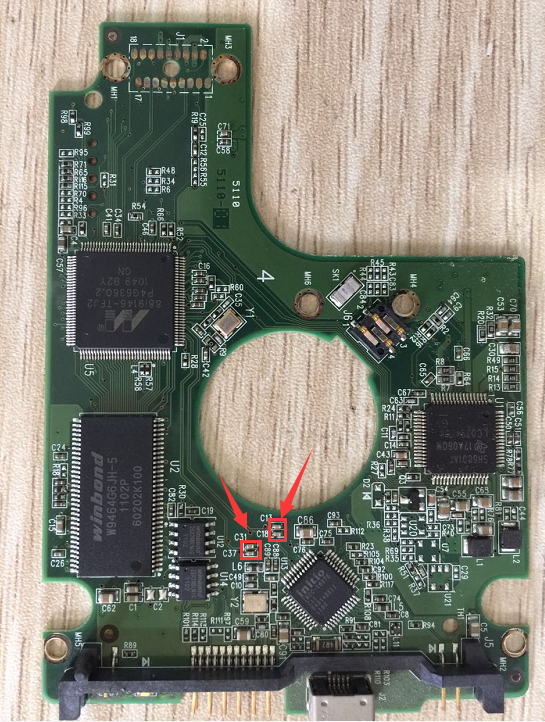
Then, we need to remove the USB PCB board, and remove the capacitors of those four points from the PCB board with a heat air gun. The location of these four capacitors are shown as follows:

One more SATA data interface is needed. We can see a SATA data interface has seven pins, three longest pins are ground electrodes, and the remaining four pins are data interface pins, of which pin 2 corresponds to E71 point, pin 3 corresponds to E72 point, pin 5 corresponds to E73 point, and pin 6 corresponds to E75 point. As shown in the picture:
Finally, we need to use wires to weld those corresponding pins and points together, and till that time, all operations are done, and the data can be transferred normally.
Part Two: How to use MRT software to recover the data from encrypted WD USB drives
We know that WD Security is a cryptographic security lock designed by Western Digital company. And this security lock is only supported on portable USB drives like My Passport and My Book. There is one encryption chip on the PCB board, so the stored data is in a state of being encrypted. That is to say, when we convert USB interface to SATA interface, the read-out data is also in an encrypted state. And in this situation, we need to use the decryption function in MRT software.
The location of USB decryption function in MRT software:
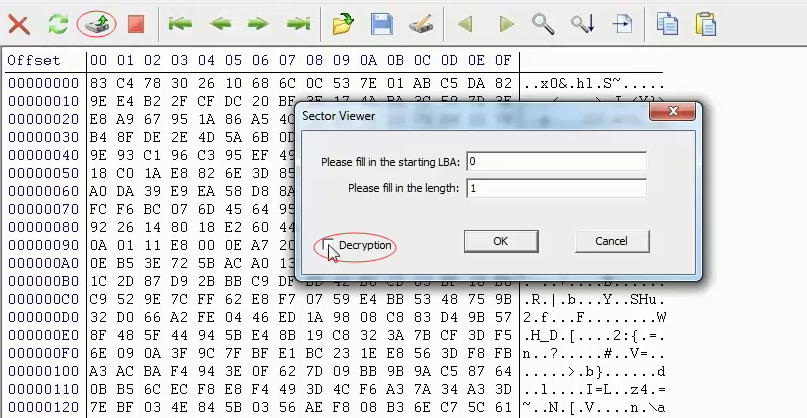
1. In WD utility, choose “Tools->User Sector Viewer” to view new sectors, there is a button named “Decryption” on the dialog box. Click this button, an interface of decryption options will pop up. Decryption will take effect when these options are set, then users can see the decrypted data when they view sectors.
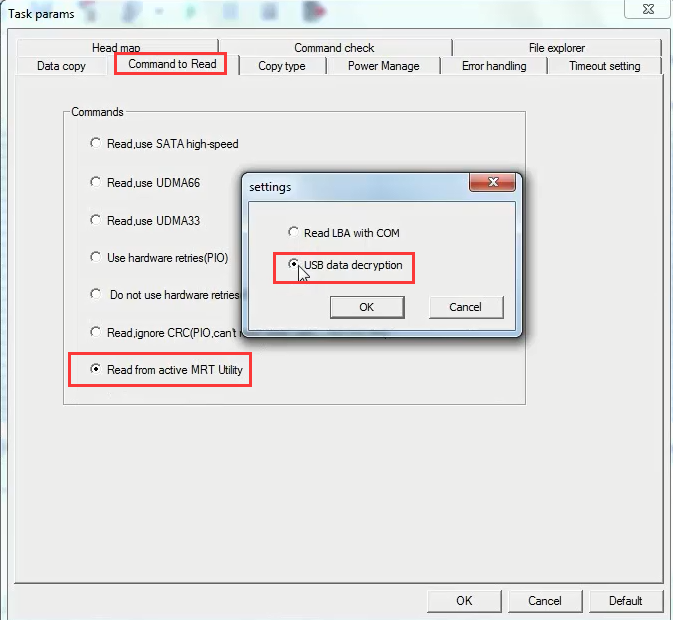
2. In “Data Explorer” utility, if we choose “Task params ->Command to Read -> Read from active MRT Utility ->USB data decryption”, then the data is decrypted when users do the image or open file system.
Introduction of USB decryption settings
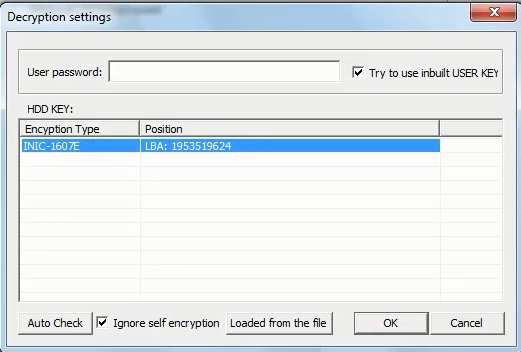
Decryption settings are not complicated. There is a user password box, input the password here if the user have set one. If not, we do not have to input anything.
There is an option named “Try to use inbuilt USER KEY” on the right, which is clicked by default. It is recommended to click this option on if the user does not input a password.
There is a HDD KEY list, WD Security cryptographic security system will store EDEK data within the disk, and EDEK data is needed when decrypting. A new KEY will be generated combined with EDEK data and user password and it will be used to decrypt the correct data out. Click “Auto Check”, EDEK data will be obtained automatically and saved as a file, so next time, we can try to use “Loaded from the file” option. When clicking “Auto Check”, if “Ignore self encryption” is not selected, software will detect this kind of KEY with first priority; if it is not selected, software will ignore the detection of the KEY type with “self encryption”. If the user does not know whether “Ignore self encryption” should be selected, we would like to suggest to click it on first, then try to read out sector 0 and see whether the data is correct or not. If the data is wrong, then click this option off, and check the data in sector 0 again. In other words, we need to try different option combinations, and use the combination which can decrypt the data successfully. Click “OK” when all options are set; and we can click “Cancel” to cancel all settings.
Decryption video link of encrypted WD USB drives:
http://us.mrtlab.com/video/wdcusbdecryptionen.rarPart Three: Retrieving user’s password of WD USB drives
Since WD Security is a cryptographic security lock with a strict encrypting and decrypting system, so there is little possibility that data recovery can be performed if the user has forgot its password. In this situation, the function of “Tools -> Retrieve user password of encrypted USB HDD” in WD utility can be used to retrieve the password, which makes it possible to recover the stored data.
The operating theory of this function is to delimit a scope based on user’s fuzzy remembrance so that our program can try to use trial-and-error method to guess the user password.
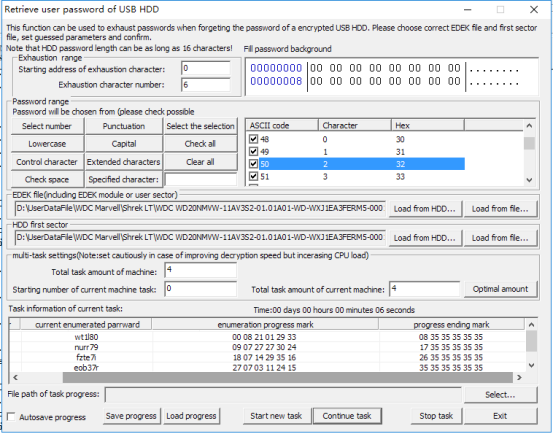
Preparation work for using the function:
1. Since the first user sector of a normally-used drive has a specified character “55AA” in the end, so the program will consider that the right password has been guessed if this character appears in the first user sector of the encrypted HDD when decrypting. Therefore, there should be the option “Load HDD first sector” when using this function.
2. What’s more, when WD Security is trying to decrypt the data, “EDED” data must be obtained. Then a new KEY will be generated combined with EDEK data and user password and it will be used to decrypt the correct data out. Therefore, there should be the option “Load EDEK file” when using this function.
3. Both the first user sector and EDEK can be obtained from the drive, but the needed first user sector should be the decrypted original one. Only in this way, can we get the correct data of the specified character when decrypting. We can use the way of converting USB PCB board to SATA PCB board to get the data and then save as a file. Then when using this function, we can select load from file, but this way will be more complex.
Guessed scope settings:
1. Explanation of character location: for example, if the password is “abcdefg”, the address of Character “a” is 0, so the address of Character “d” is 3.
2. Setting rules of guessed scope: for example, if the password is “abcdefg”, and we can only remember the first three characters, so we can input “abc” in “Fill password background characters with (hex)” and input “3” in “Starting address of exhaustion character” and fill “4” in “Exhaustion character number”. If we forget “abc” but remember “defg”, then we need to leave the first three characters blank and input “defg” in “Fill password background characters with (hex)” and input “0” in “Starting address of exhaustion character” and fill “3” in “Exhaustion character number”.
3. What we have mentioned above is the starting address and length of the guessed password, and the filling requirements of the guessed character. Next we are going to set the characters that may appear in the guessed password. In the panel list, all the alphabets, numbers and specific characters are included and selected by default. If the guessed password only includes numbers or minuscules, then other characters can be cleared and we just need to select numbers or minuscules. If some specified characters are remembered, they can be filled in “specified character” and separated with coma, such as “1,2,a,b”; then click to select “specified character” to make these characters selected in the list.
Multi-machine and multi-task settings:
If only one machine is needed and no special requirements, we can directly use the default settings.
For the task amount of current machine, it is better to use the default number which is set according to the CPU core number. If the number is less than the default number, it will decrease the efficiency. And if the number is more than the default number, it will bring little benefits either. However, if we do not want this function to occupy so much CPU resources, we can decrease the number. If there is just one machine, then the number needs to be consistent with the actual number.
When we need to retrieve the password with more than one machine simultaneously, we can refer to the way below:
If we need eight tasks and two machines to work at the same time, the “Total task amount of machine” should be filled with “8” for both of the two machines. At this time, if both the two machines are assigned with four tasks, “Stating number of current machine task” should be filled with “0” for the first machine and “4” for the second machine.
If the “Total task amount of current machine” is “2” for the first machine, the “Stating number of current machine task” should be filled with “2” and the “Total task amount of current machine” for the second machine should be “6”.
Rules: when the task of more than one machine is being set, “Total task amount of machine” should be consistent for every machine. “Stating number of current machine task” of the machine behind is the sum of the total task amount of all the machines.
Viewing, saving and loading progress:
It may take a long time to do the task of guessing a password. Therefore, viewing progress can let us know the progress. Saving and loading progress can make it possible to stop the task and save the task progress when it is not convenient for us. And when we need to continue the task, we can load the progress again.
Instructions of viewing progress:
If there are five characters to enumerate and all minuscules, 26 alphabets, are selected, the alphabets will be arranged randomly at the place of the five characters until all possibilities are tested. If there is just one task, then the task progress will be performed from 0,0,0,0,0 ->0,0,0,0,1->0,0,0,0,2 … ->0,0,0,0,26 -> 0,0,0,1,0 … >0,0,0,1,26 to 26,26,26,26. When the first number becomes 1, the whole progress has performed 1/26.
The time the task has taken will show above the progress list. We can estimate the whole time of completing the guessing task according to the shown time and the task progress.
Decryption video link of encrypted WD USB drives:
http://us.mrtlab.com/video/wdcusbdecryptionen.rarThe above all are the contents of advanced data recovery tutorial of encrypted WD USB drives, thanks for your reading.
MRT Sales consultant--Pink
Email:
sales@mrtlab.comSkype:
sales@mrtlab.comQQ:3292109557



